What is a Hardened Baseline Configuration?
Hardened Baseline Configuration is a crucial aspect of system security for cybersecurity experts and the risk management teams. The secure baseline configuration represents a set of security controls that have been carefully selected and implemented to provide a robust general level of system hardening.
There isn’t a one-size-fits-all solution, and specific configurations will vary depending on the type of system (server, desktop, etc.), role and its intended use.
What are CIS Benchmarks?
CIS Benchmarks are prescriptive configuration recommendations for over 25 vendor product families, categorized into seven groups. These include Operating System Benchmarks, which cover security configurations of core operating systems like Microsoft Windows, Linux, and Apple OSX, ensuring compliance requirements with security standards.
Learn more about CIS Benchmarks: HERE
What are CIS Controls?
CIS Controls provide a structured framework of security best practices that guide organizations in effectively configuring their systems and enhancing overall security. CIS Controls provide a prioritized set of security best practices for system hardening broken into 18 Controls with each having their own safeguard for cyber hygiene and Implementation Groups (IGs) and prioritization.
Learn more about CIS Controls: HERE
What are CIS Build Kits?
The CIS Build Kits are resources that help organizations implement secure configurations more quickly. They are automated, efficient, repeatable, and scalable. They can be applied via the group policy management console in Windows or through a shell script in Linux (Unix,*nix) environments. They can be customized to an organization's particular use case. CIS Build Kits offer pre-configured templates and guidelines for system hardening to streamline the process and improve security.
What is CIS SCAT?
CIS SCAT stands for CIS Controls Self Assessment Tool. It is a web application that enables security leaders to track and prioritize their implementation of the CIS Controls. There are two versions of CIS CSAT: Pro and Hosted.
CIS CSAT Pro is the on-premises version of the tool and is available exclusively to CIS SecureSuite Members.
CIS-hosted CSAT is a web-based portal version of CSAT hosted by CIS. It is free to every organization for use in a non-commercial capacity to conduct an assessment of their organization’s own implementation of the CIS Controls
CIS also released a CIS CSAT Ransomware Business Impact Analysis tool. This allows organizations to evaluate their likelihood of experiencing a ransomware attack and its potential impacts by using the CIS CSAT Ransomware Business Impact Analysis (BIA) tool.
What is CIS-CAT Pro?
CIS-CAT Pro is a configuration assessment tool supporting both host-based and remote assessments. To assess remote endpoints, the target system must be configured for remote connections. CIS-CAT Pro Assessor, a Java-based tool, scans your system’s configuration settings to evaluate compliance with CIS Benchmarks, aiding in configuration management and practices for securing your environment.
What is CIS RAM?
The Center for Internet Security Risk Assessment Method (CIS RAM) is a methodology designed to assist organizations in implementing and evaluating their information security risk posture in relation to the CIS Critical Security Controls (CIS Controls). The CIS RAM Family of Documents offers a comprehensive set of resources, including instructions, examples, templates, and exercises, to facilitate the process of conducting a thorough cyber risk assessment.
CIS RAM offers three distinct security approaches tailored to accommodate varying levels of organizational capability. The three approaches are tailored for Novice, Experienced or Expert cybersecurity personnel. CIS RAM assists in identifying and addressing vulnerabilities through its risk assessment methodology, contributing to effective system hardening.
What are CIS Hardened Images?
CIS Hardened Images are virtual machine (VM) images that are pre-configured to meet the robust security recommendations of the associated CIS Benchmark for that operating system. These VMs built to CIS Benchmarks standards can help organizations meet compliance with common frameworks like NIST, HIPAA, PCI DSS, DISA STIGs, and more. CIS Hardened Images provide pre-hardened and securely configured operating system and software images to aid in system hardening and enhance security.
Does CIS have Cybersecurity Best Practices?
CIS publishes a wide range of resources, including whitepapers, case studies, and guides, to help organizations improve their cybersecurity practices. They focus on emerging threats, trends, and solutions to provide valuable insights to the cybersecurity community.
What is ISAC?
The Information Sharing and Analysis Center (ISAC) is an organization that collects, analyzes, and shares actionable threat information with its members. It also provides them with tools to mitigate risks and improve resiliency. CIS facilitates information sharing and collaboration among its members and partners. They host conferences, workshops, and webinars to foster communication and knowledge exchange within the cybersecurity industry.
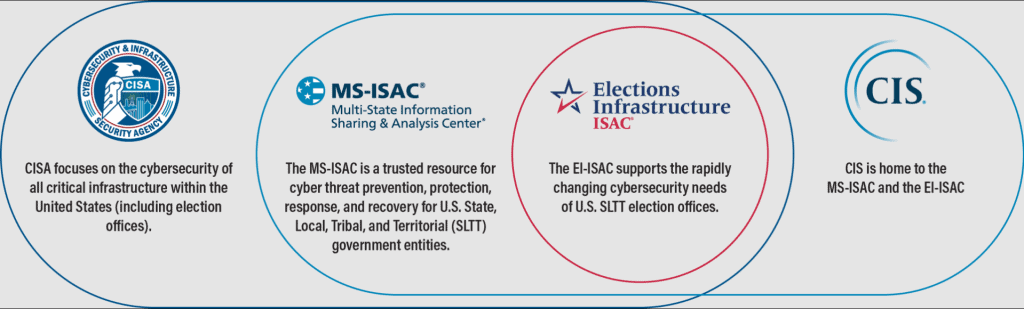
The Multi-State Information Sharing and Analysis Center (MS-ISAC) and the Elections Infrastructure Information Sharing and Analysis Center (EI-ISAC) are both part of the Center for Internet Security (CIS). They provide a variety of services that augment and enhance members' cybersecurity teams.
Resource: CIS ISAC
What are the CIS SecureSuite Membership benefits?
CIS SecureSuite: CIS offers a subscription-based service called CIS SecureSuite, which provides access to various cybersecurity tools and resources. Members can quickly and effectively assess endpoint configurations, measure compliance to the CIS Benchmarks, and conduct, track, and assess their implementation of the CIS Critical Security Controls (CIS Controls). Additionally, members have access to CIS-CAT Pro which is a configuration assessment tool that scans systems and reports on their levels of compliance with the best practices of the CIS Benchmarks and CIS Controls.
Learn More HERE
Why automation is important when system hardening?
Some CIS Benchmarks exceed 1,000 pages and offer hundreds of recommendations. Applying these benchmarks to each server environment, role, and version is time-consuming. Additionally, creating a lab environment to simulate the impact of security policies on servers and network devices is labor-intensive and costly, but essential to prevent data breaches.
CalCom Hardening Suite (CHS) is an automated solution for server hardening, with the goal of enhancing server security and compliance while reducing operational expenses. By assessing the effects of security hardening modifications on production services, CHS establishes a robust, continuously fortified, and actively monitored server environment. CHS enforces server security policies in real time, thus, ensuring that the servers are proactively protected.
CalCom is also a CIS SecureSuite Member which means that your entire enterprise IT estate can be audited against the range of CIS Benchmarks. Ask for a FREE DEMO to learn more.