Microsoft continues urging its customers to understand two core security vulnerabilities in the domain controllers of Active Directory. These vulnerabilities had been addressed by the company in November 2021. It was followed by a PoC or Proof of Concept tool on 12th December.
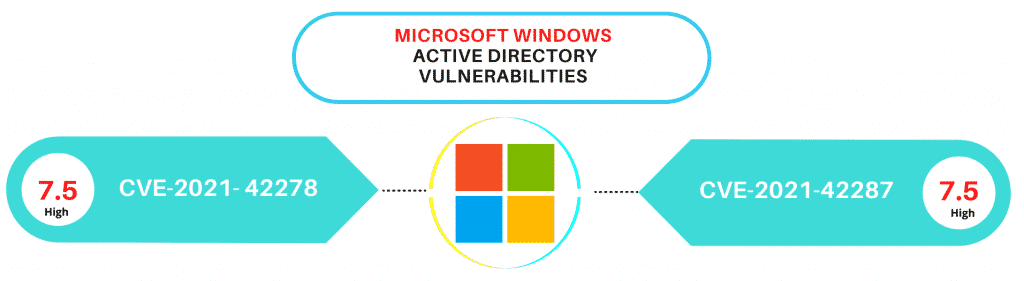
The two vulnerabilities have been tracked as CVE-2021-42278 sAM (sAMAccountName spoofing ) and CVE-2021-42287 KDC. These vulnerabilities feature a severity rating of 7.5 out of 10. These are concerned with a privilege flaw that tends to affect the AD DS or Active Directory Domain Services component. Andrew Bartlett from Catalyst IT has been accredited with discovering and reporting both the vulnerabilities.
Understanding the Active Directory Vulnerabilities
Active Directory is Microsoft's directory service that is implemented on the Microsoft Windows Server. The component is used for the purpose of access and identity management. While leading tech giants have marked the vulnerabilities as 'exploitation less likely' in their subsequent assessments, PoC's public disclosure has made way for renewed calls. These calls are aimed at using the necessary fixes towards mitigating any prospective exploitation by respective threat actors.
The CVE-2021-42278 SAM vulnerability allows the attacker to make changes to the attribute of SAM-Account-Name. The attribute is used for logging a user into subsequent systems in the domain of Active Directory. On the other hand, with CVE-2021-42287 KDC vulnerability, it is possible to imitate the domain controllers. This helps in granting some bad actor with relevant domain user credentials for gaining access as the user of the domain admin.
When an attacker is able to combine both the vulnerabilities, it is possible to carve a simple path to the user of the Domain Admin in the Active Directory environment not using these updates. The escalation attack enables attackers to easily elevate the privilege to that of the Domain Admin once they have compromised any regular user in the domain.
Identifying the Vulnerabilities in Active Directory
- Click View > Advanced Features
- Open the properties of an object > Attribute Editor tab > Scroll down to sAMAccountName
Establishing secure configurations
Microsoft keeps searching for effective ways to combat such vulnerabilities. According to the CIS Critical Security Controls - Control 4 discussing Secure Configuration of Enterprise Assets and Software states a complete software inventory is a critical foundation due to attackers continuously looking for vulnerable versions of software to be remotely exploited.
Implementing a secure configuration to achieve compliance and better security posture while maintaining it in an organization's changing network environment is impossible without the right tools and using automation. Creating a lab environment that will try to simulate the production environment and performing tests on it is labor-intensive and will not completely cover you from the risk of outages.
CalCom's Hardening Solution (CHS) will learn your network and report to you which policy rule will result in breaking production and why. It will then automatically implement your desired policy over your entire infrastructure, from a centralized management point. Finally, CHS will keep your assets continuously hardened, preventing these often missed compliance drifts that often lead to audit failure on breaches.




